Chaos and Order
05 February 2020
I have too much going on. In the last 15 minutes before writing this I thought about 3 work projects, legal paperwork, trip planning, house repairs, what I’m going to cook, and helping a friend move.
My life is a careful balance of chaos and order.
Creativity is chaotic. My thoughts are scattered and rapid when I’m puzzling through a work problem or making notes for music. My best ideas come in the shower, or when I’m daydreaming.
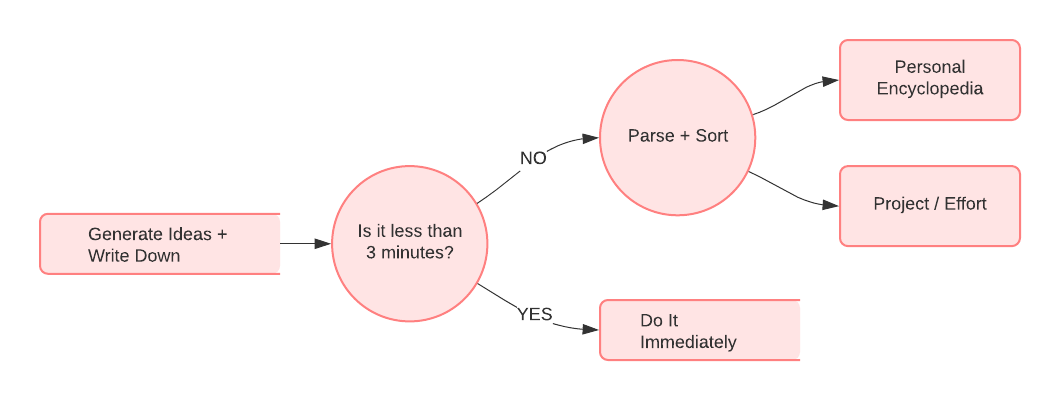
When I have a new idea, I need to retain everything. It’s not organized, so I need to capture unstructured information.
However, incoherent information isn’t useful on its own. It’s only after I process it that my ideas are effective. Creating order from chaos is an essential second step.
Requirements for Chaos
Chaotic systems have structure.

Good ideas show up all the time. They’re transient, and unpredictably structured. A system to collect chaotic information must:
- Support unstructured information
- Be accessible all the time
- Be very quick
- Be simple
There arethings that are not required:
- Easy to share
- Permanant
- Searchable
I found a great tool for this, the ‘World’s Oldest Data Structure’.

Paper. You read that right. Paper.

I always carry paper and a pen. It’s highly accessible, practically free, secure, quick, and flexible. It supports text, diagrams, music, even mind maps. My friends laugh and smile, presumably in admiration.
Order from Chaos
Random notes must be turned into something, like grist for the mill. I have a simple method:
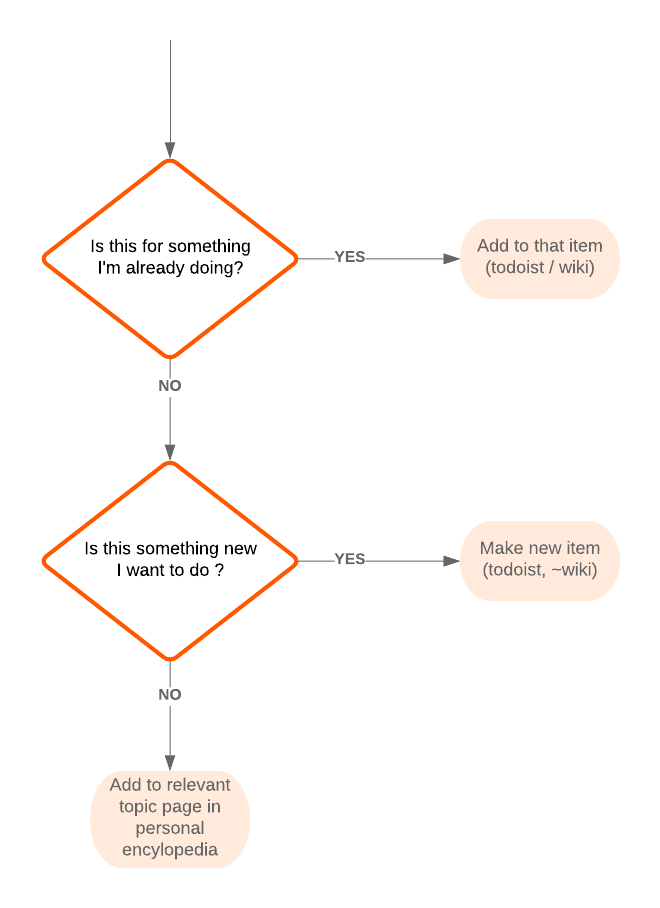
I’m Already Doing It
The most common note is for an existing project: a work effort, piece of music, or discussion with a friend. I’ll have a Todoist project, wiki page, or email thread going, so I add the note into it.
Something New to Do
Let’s say I have a note for something new. I’ll create a new entry in an existing system, perhaps a single Todoist task, a recurring, or a wiki page. Then I’ll go through my memory palace and copy over anything relevant.
Maybe Someday
This is where I put everything else. If I’m not going to use it in the near future, I add the note to a wiki page. This system makes assumptions:
- Don’t discard anything. I’m not phlegmatic about losing data
- It is easy to adjust
- It is quick. I process notes several times a day.
I’m accreting knowledge. Ensembling is powerful; just look at the wisdom of crowds.
Why all the fuss? Because people are chaos and order. Life is order and chaos. I try to embrace that, one step at a time, using paper.
What do you do?
PermalinkTaming the White Whale - Email
28 January 2020
How do I coordinate with 8 people in different groups? How does an airline tell me about changes to next week’s flight? What’s a good way for a long-lost friend to reach me?
The most popular online communication tool is one of the oldest: email. It’s used for everythig: personal messages, alerts, marketing, etc.
Email is a beast that follows our every footstep.
Its flexibility makes it a challenge. I get emails with varying mental and time requirements. How can I process the emails I receive? How can I send emails that gets me the responses I’m looking for?
I want to organize my communication, and make it optimally useful at minimal cost.*
Context
Email sits in the intersection of security, identity, privacy, communication, and human perception.
There are assumptions we make:
- Only I can read my email
- I can contact someone via email and only they will see it
- I can store emails in my account and they will be secure
- It’s a good way to send information to people
- It’s a good way for people to send information to me
Consider identity. I bet you have an email address, or more than one. They are part of your identity. Heck, you may advertise them on your blog, or a business card.
Second, ubiquity. Email has powerful network effects and utility. Anyone can contact you, and you can respond to them instantly. Network effects influence your life.
What about privacy? Someone can find your email address by Googling your name. Email is a public way to contact you. Your phone number and physical address have some expectation of privacy. Your email address, not so much.
Security is a big consideration. Institutions you interact with use email to authenticate you. For example, online banking requires an email address. Your phone company, landlord, and airline all know it.
If I had nefarious intentions, knowing your email address gives me a way to target you. It’s the skeleton key to your online life. Good email security fundamentals are critical.
Uses
I categorize email by its intended use:
- Personal communication - sending messages to loved ones. This is the closest analogy to writing a personal letter & mailin it.
- Work communication - sending/receiving messages, often for coordination purposes. This is being superseded by messaging applications like Slack.
- Personal notes - reminders to myself, e.g.
Get coffee on the way home,put $ into savings tonight, orremember your passport - Reference - Useful details, often within a specific timeframe. Plane ticket confirmations are a great example.
- Alerts - Important + infrequent automated messages. Bank fraud warnings are one example.
- Unwanted - Spam. Phishing attempts. Contact from companies you may have interacted with, but don’t want to hear from again. This is 99% of the email you receive; thank goodness for spam filters.
[ ](https://en.wikipedia.org/wiki/Spam_(Monty_Python)
](https://en.wikipedia.org/wiki/Spam_(Monty_Python)
Some of these intended uses overlap. Others conflict.
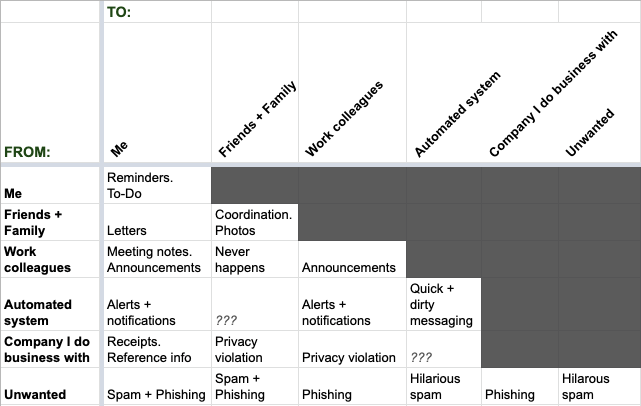
Let’s categorize the way I use email a differetn way, by sources and destinations:
Interaction Patterns
There are common email interaction patterns:
Quick Items
I use email to send quick messages, alerts, or announcements. These messages take only a few minutes to resolve.
Search
Some emails are a knowledgebase. This is common; that’s why Gmail’s main interface is search.
Threads
Modern email apps group a conversation into a thread, so it’s shown together. This is a great idea.
Timing
An email is often useful at a certain time. For example, that email confirmation about my flight? I want receive it soon after booking, and then ‘snooze’ it until a few days before I travel. It’s clutter in the interim.
A missive from a friend, on the other hand? I want to see it immediately.
Make Tools Yours
Tools are for your use. They should suit your needs, not the other way around.
I use different email accounts for different purposes: for friends, for work, and for my career. Each account has different settings for notifications, app integration, and privacy.
Communication
Email is a tool for transmitting text. This has great advantages (permanence, legibility). It also has drawbacks (tone of voice, no body language). There’s a margin of error, and it’s pretty big. Words are ambiguous. Connotations and idioms are not universal.
With any communication tool, there is a gap between what you intend to say and what people perceive.
People don’t read email. Many people spend < 60 seconds reading an email. Many things compete for our attention; giving everything short shrift is natural.
Email suffers from the timing and frequency constraints that bedevil all communication. Being effective is key.
Here’s what I do:
- Keep it short. Shorter. Even shorter than that.
- “Is this the minimal length that has necessary info?”
- Put the important details at the top, in bullet points
- Message only when necessary. Repetition breeds disregard
- Long emails are ignored. Go for clarity & brevity. If elaborate details are important, do it by voice. The bandwidth is far higher.
- No ambiguity. I use inside jokes, but only with people who know them.
Email is useful sometimes:
- “Can the recipient resolve this in < 3 minutes?”
- “Does this need minimal interaction?”
- Back-and-forth is messaging. Anything else, and use high-bandwidth voice.
- “Will this person need to find this in several days?”
I use standard formats:
Work Communication
Tl;dr - <one-sentence summary>
The Long Version:
<background>
<process + data>
<result>
Announcements + Notifications
I send announcements at times.
Hey folks, here's the details for <event/subject>
* When -
* Where -
* What to Bring -
* Important Topic -
The consistency and format works well for distracted people.

Search
Search is a different beast; my words interact with a search utility, and not a human.
I use keywords. If I’m writing about a trip to LA in March, I’ll include words like ‘family’, ‘flight’, ‘travel’, ‘itinerary’, ‘March’, ‘California’, ‘LA’, and ‘Los Angeles’.
I can search using key words/phrases to find this email, quickly. This is an old trick. If you get an email with a plane ticket confirmation, or an Amazon order, it has key words & phrases in it.
To-Do
These are very short. For example, today I wrote a reminder to myself, to get my niece some books:
niece books
…that’s it. Just enough to jog my memory. I’ll route it into my to-do system later.
Email is a tool. Its effects depend on our intentions, and our methods.
I use email in specific ways because I’m perennially busy. I’d rather spend my time on better problems than puzzling out the optimal format for each email.
How do you use email?
Permalink